Related news
We have talked at length about the security of our phone on Android and how it can be improved. Especially that even if Google puts all possible measures in the Google Play Store, in the end, we will always have in hand the decision to install an APK.
And it is that recently, it was discovered, via Arstechnica, that a series of applications, downloaded over 300 thousand times from the Play Store, with Trojans in their guts, they have stolen passwords, two-step authentication codes, and even screenshots of users.
Common applications that hide Trojans
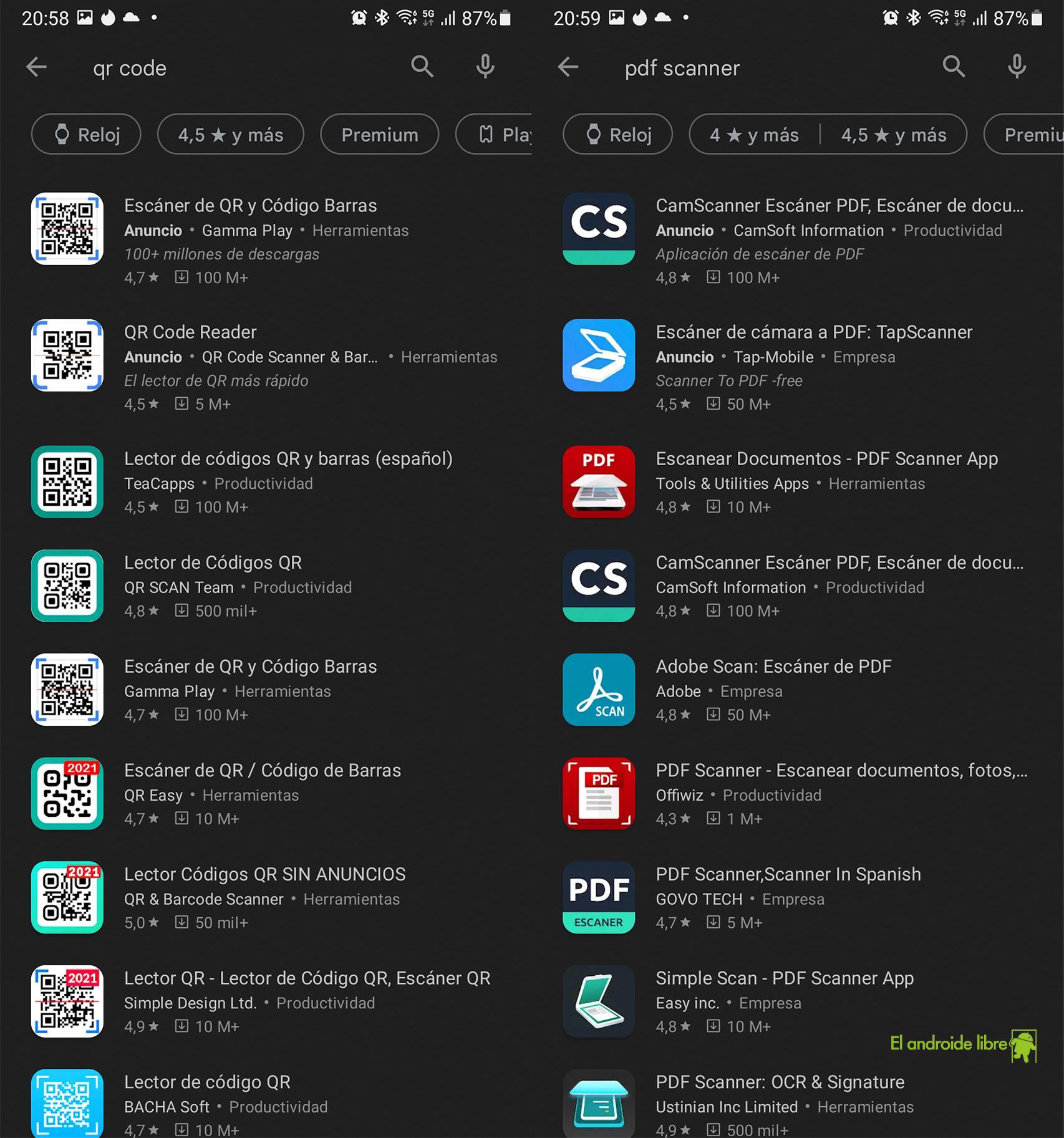
These applications were from QR code readers to the same PDF scanner, which are part of four types of malware families that have been distributed for four months through the Android media store.
QR code reader apps
Free Android
Some apps have used a series of tricks to bypass restrictions imposed by the Google Play Store. These restrictions include the prohibition on the use of accessibility services for people with reduced visibility
What is really difficult from a machine learning perspective to tackle these type of Trojans is the download from third-party sources when an application installed on the phone requests it. The user accepts and the download begins.
google play
Free Android
These apps do not include no malware detection, it is therefore up to us to assess whether the file that we are going to transmit to the internal memory of our Android phone comes from a source that we trust.
When to install an APK
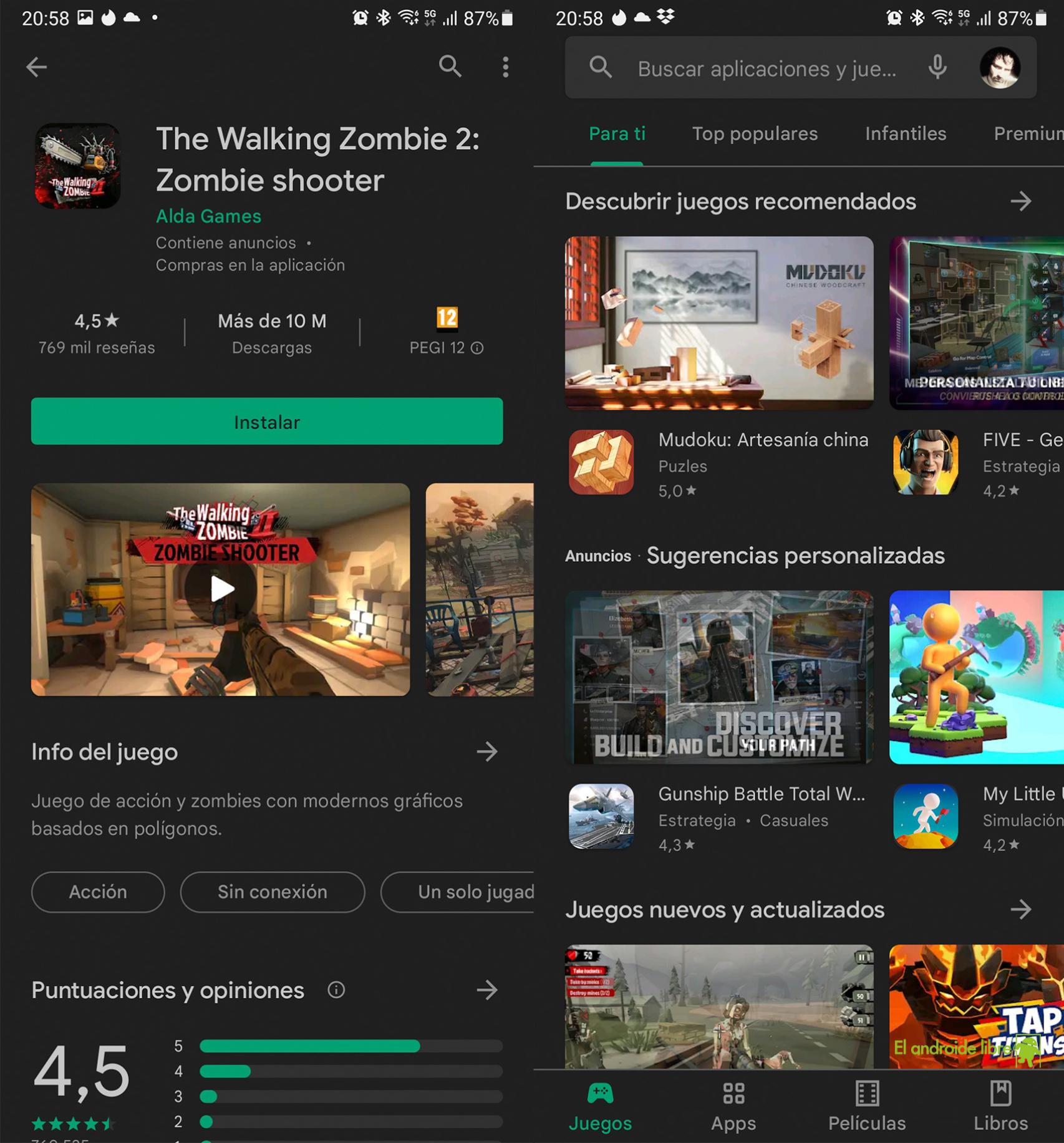
Surely you have downloaded one of the latest games from the most famous companies such as Supercell, Netease or Tencent Games itself.
We download the game from the Google Play Store, and when we start it, after some welcome screens, the the game requires our approval to unload most of the size of its total weight.
PUBG: New State requests update
Free Android
This ranges from one to several gigabytes of data. Something that can be understood that if we search for its origin, it is easy to think that we are dealing with a company that we can trust.
Another thing would be for us to have a similar experience of an app that we downloaded and from which we do not know who is really behind. We can take the example of these QR code reading apps, which are very practical, but you have to stop for a moment to know where they come from; always have alternatives from the same Google.
When not
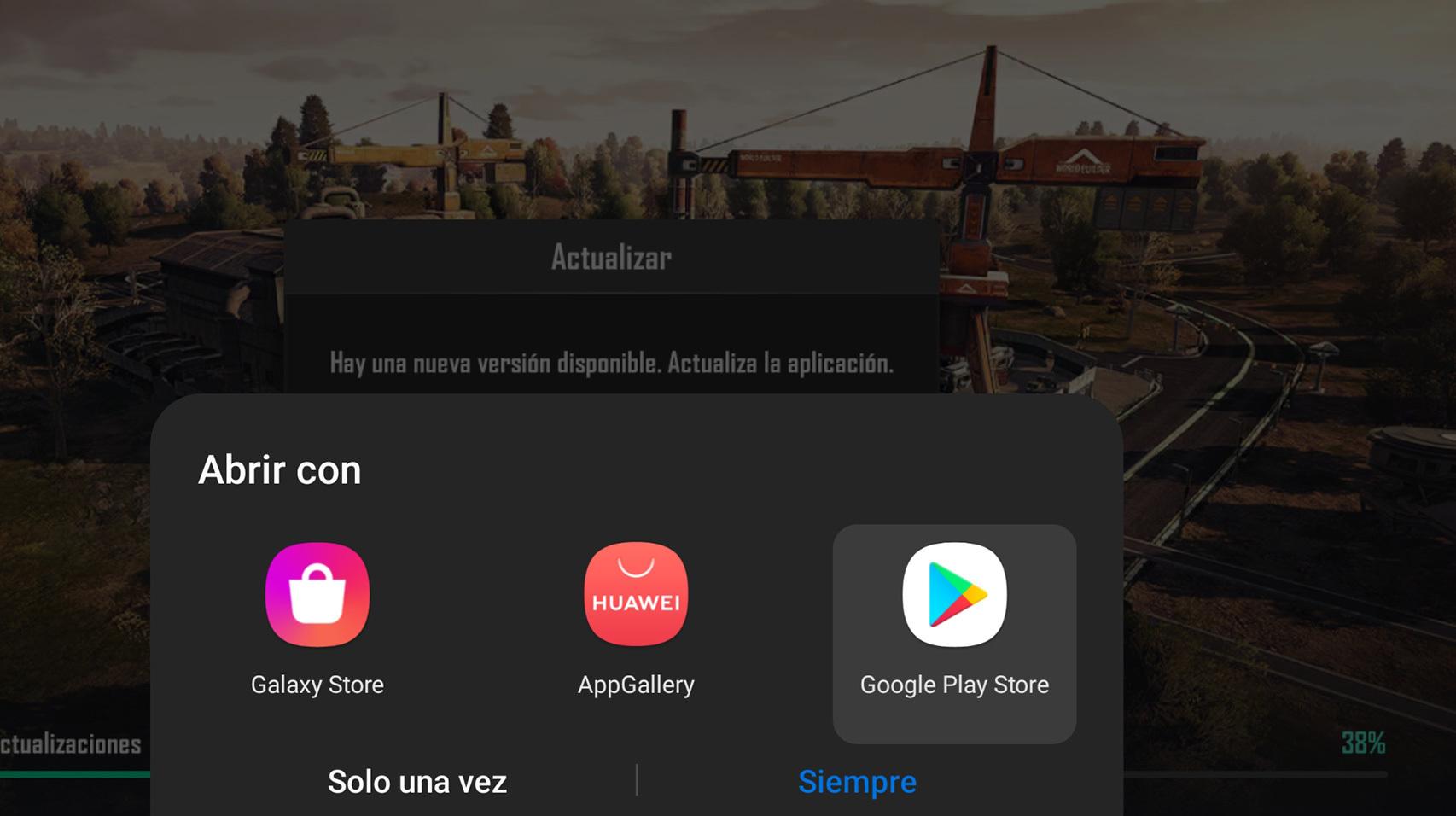
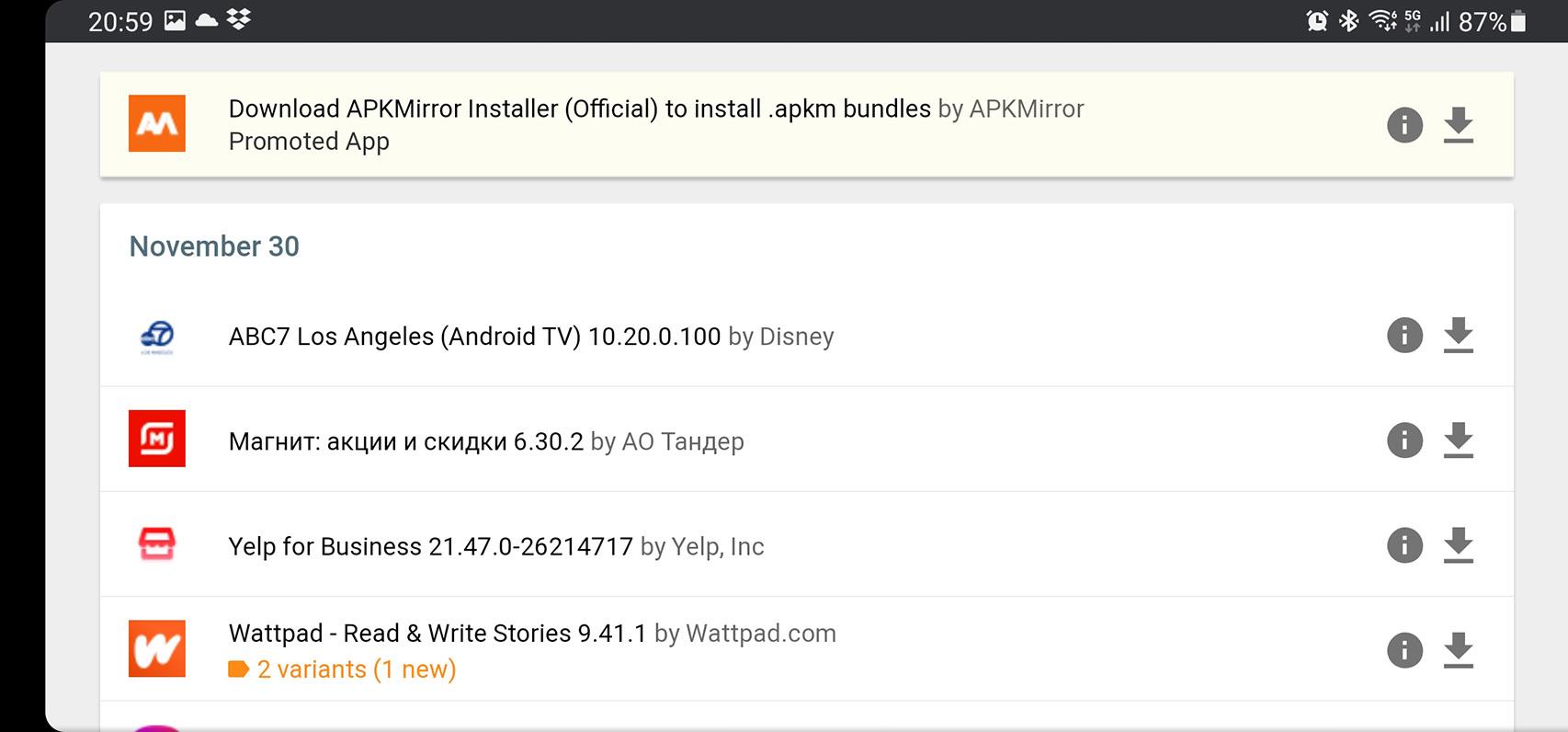
The most obvious case of an app that may ask us to download data from third-party sources is the one dedicated to being a repository of APK or third-party stores.
Apkmirror is a trusted repository
Free Android
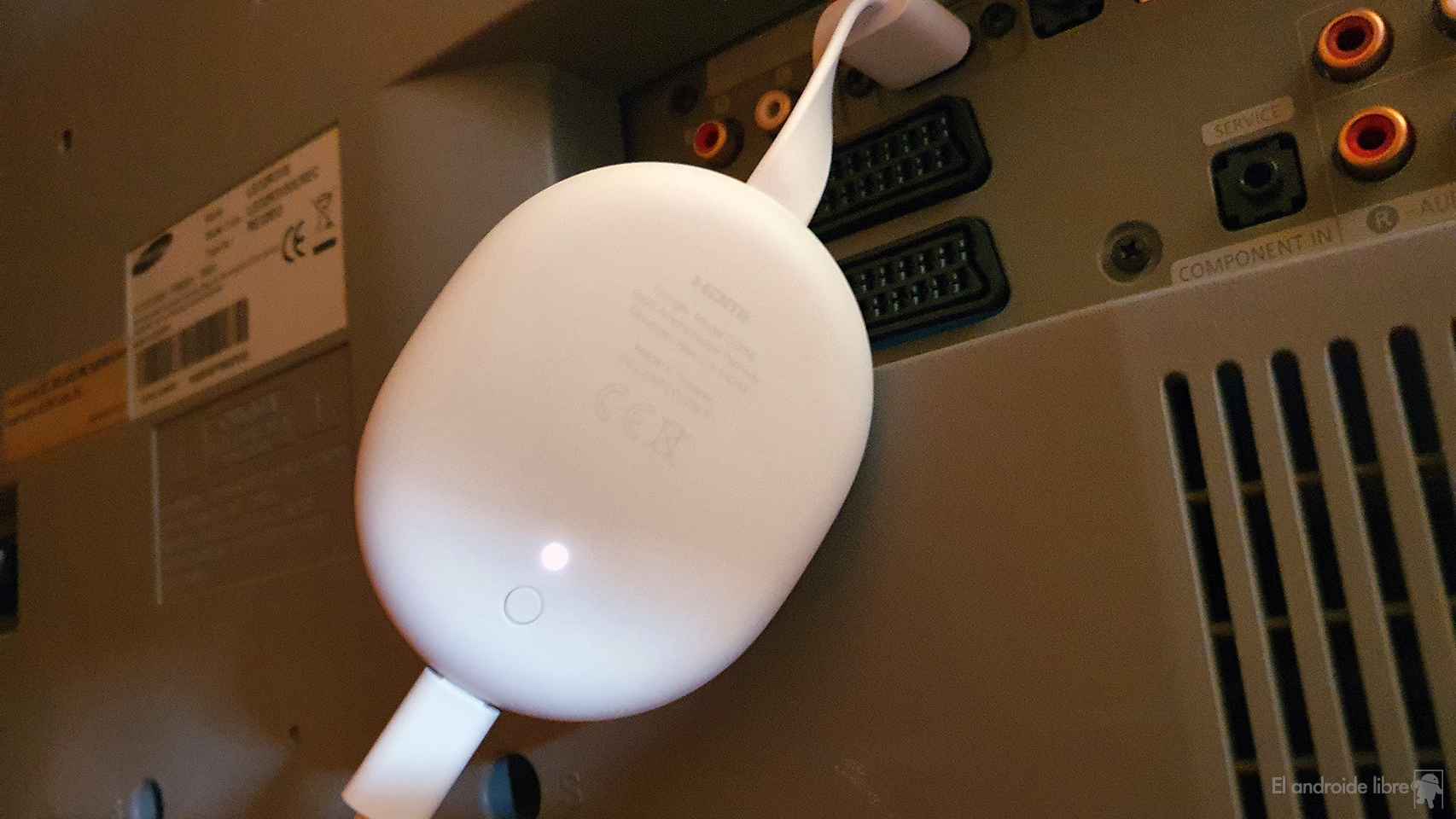
You can fully trust apkmirror or uptodown (a Spanish company), just like F-Droid, Aptoide or APKPure. There are also as many as the same Huawei AppGallery; the means downloading your entire catalog
But the the problem comes from many other repositories who, in the heat of these sayings, offer their services to download the latest apk of this game that we can play before anyone else. Here, you would have to think twice and resist a bit to hope that this APK is available in some of the aforementioned.
The Huawei app is another trusted site
Free Android
And this is it those in a hurry have never been good advisers, a saying that can be used today to be silent and not install unwanted APKs.
That is to say it is in our power to accept the request to download more data or this APK and thus let in this malware disguised as these applications that we all usually use.
Using a small head and google search We put the name of the publisher of the app in the Google Play Store or any repository to check if it is a recognized repository.
it may interest you
Follow the topics that interest you
.
Table of Contents